You are the network administrator for All network servers run Windows Server 2003. A member server named TESTKING1 hosts several hundred folders, which reside in various locations on the server. TESTKING1 is configured to run a normal backup of the folder every Saturday at 1:00 A.M. You discover that users edit the contents of the folders on Saturday and Sunday. You need to use the Backup utility to reschedule the backup job so that it runs every Monday at 1:00 A.M. instead of every Saturday at 1:00 A.M. You must achieve this goal by using the minimum amount of administrative effort. What should you do?()
A、Specify Monday as the start date of the job.
B、Reconfigure the job schedule to run the backup every Monday at 1:00 a.m.
C、Add an additional schedule to the job. Configure the additional schedule to run the backup on Monday at 1:00 a.m.
D、Use the Repeat Task option to configure the existing job to repeat every 48 hours until an interval of 336 hours passes.
具有温中止痛、杀虫功效,治疗蛔虫腹痛、呕吐或吐蛔,应选用的药物是()
A、干姜
B、吴茱萸
C、砂仁
D、小茴香
E、花椒
患者,女,27岁。妊娠两月余,不慎跌跤,小腹刺痛,阴部渗红,用药应首选的药物是()
A、杜仲
B、续断
C、桑寄生
D、艾叶
E、白术
Your network consists of a single Active Directory domain. All network servers run Windows Server 2003 Service Pack 2 (SP2). The domain includes two global groups named ResearchManagers and ResearchUsers. You create a share named ResearchData. On the ResearchData share, you assign the Change permission to ResearchUsers and ResearchManagers. The ResearchData folder contains a file named ResearchConfidential.rtf. The permissions for ResearchConfidential.rtf are configured as shown in the exhibit. (Click the Exhibit button.) 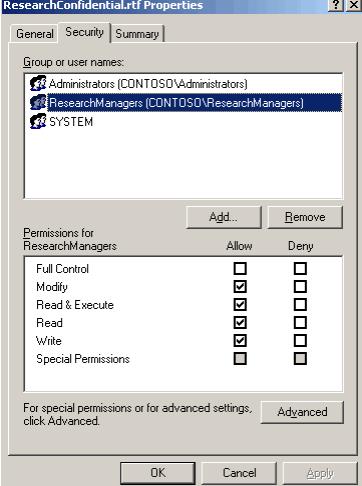 Members of ResearchUsers report that when they try to open ResearchConfidential.rtf, they receive an access denied message. Users report that they can add and modify other files in ResearchData. You need to ensure that ResearchUsers members can open ResearchConfidential.rtf. The solution must prevent ResearchUsers members from modifying the file. What should you do?()
Members of ResearchUsers report that when they try to open ResearchConfidential.rtf, they receive an access denied message. Users report that they can add and modify other files in ResearchData. You need to ensure that ResearchUsers members can open ResearchConfidential.rtf. The solution must prevent ResearchUsers members from modifying the file. What should you do?()
A、 On ResearchData, enable permission inheritance.
B、 On ResearchConfidential.rtf, enable permission inheritance.
C、 On ResearchData, assign the Read permission to ResearchUsers.
D、 On ResearchConfidential.rtf, assign the Read permission to ResearchUsers.
Server1 contains a folder named D:/Salesdata, which contains important company data. The hardware-monitoring software reports that the disk that contains volume D is in danger of imminent disk failure. You order a replacement disk, but you must wait at least one day for the disk to be delivered. You discover that you do not have a backup of the D:/Salesdata folder because a recent backup was configured incorrectly. You need to back up the D:/Salesdata folder so that you can restore the data if the disk fails. You need to achieve this goal as quickly as possible. What should you do? ()
A、Perform a normal backup of the D:/Salesdata folder.
B、Perform an incremental backup of the D:/Salesdata folder.
C、Perform a differential backup of the D:/Salesdata folder.
D、Perform a daily backup of the D:/Salesdata folder.
E、Enable Shadow Copies on volume D:/Configure the shadow copy location as C:/.
You are a network administrator for your company. All servers run Windows Server 2003. You manage a server that functions as a file server. The data volume on the server is mirrored. Each physical disk is on a separate controller. One of the hard disks that contains the data volume fails. You discover that the failure was caused by a faulty SCSI controller. You replace the SCSI controller. You need to restore the data volume to its previous state. You need to achieve this goal by using the minimum amount of administrative effort. What should you do?()
A、Run the diskpart active command to activate the failed volume.
B、Convert both disks to basic disks, and then restore the data.
C、Break the mirror, and then re-create the mirror.
D、Select a disk in the mirror, and then reactivate the volume.